Know your attack surface & vulnerabilities before they’re exploited.
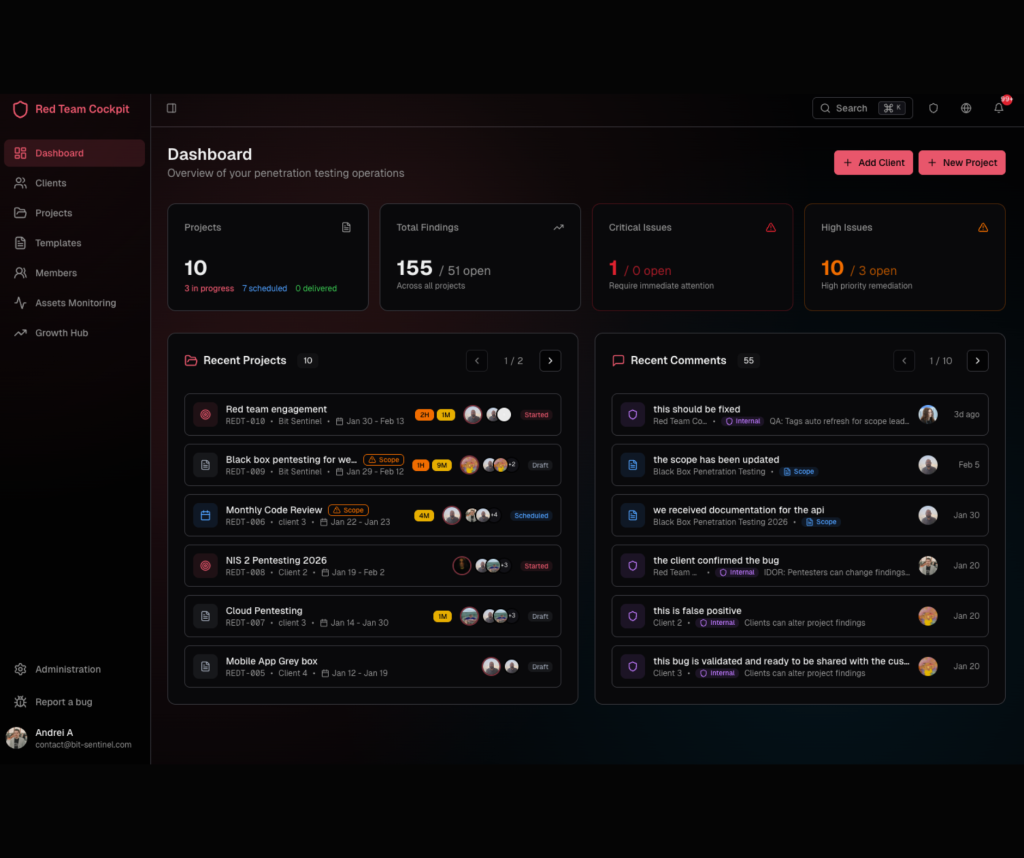
A purpose-built Red Team platform that enables organizations to test real-world attack paths, validate security controls, identify exploitable vulnerabilities, and translate technical findings into actionable risk reduction.
The challenges you face
Security doesn’t fail from lack of effort - it fails from lack of clarity. These are the operational challenges we help organizations overcome every day.
Reports that collect dust
Security assessments delivered as static PDFs that are outdated before they're read.
No clear prioritization
Hundreds of findings with no guidance on what actually matters to your business.
Verification bottlenecks
Waiting weeks to confirm if your patches actually resolved the vulnerabilities.
Limited visibility
No insight into assessment progress or real-time security posture changes.
Siloed communication
Critical findings lost in email chains, unclear escalation paths.
Scope confusion
Misaligned expectations between what was tested and what you needed tested.
Security assessments that drive real improvement
Our platform ensures you get more than just a PDF. You get clarity, actionable insights, and ongoing visibility.
Reports your team can use
Dynamic dashboards that translate technical findings into business risk. See exactly what's at stake and what to fix first.
- Risk-based prioritization
- Executive summaries
- Remediation timelines
Risk-based prioritization
Every finding scored by real-world exploitability and business impact. Focus your limited resources on what truly matters.
- CVSS enrichment
- Business context scoring
- Attack path analysis
Real-time visibility
Watch your security posture improve as you fix issues. Track assessment progress and see your security score evolve.
- Live status updates
- Progress tracking
- Trend analysis
Collaborative scope definition
Define scope together, adjust on the fly, and ensure every engagement tests what matters most to your organization.
- Interactive scoping
- Asset management
- Test case library
Track your progress
View the assessment timeline, track remediation status, and measure your security posture improvement over time.
- Milestone tracking
- Burndown charts
- Historical comparison
Enterprise-grade security
Your vulnerability data is protected with the same standards we recommend to you. Bank-grade encryption and access controls.
- AES-256 encryption
- Role-based access
- Full audit logs
Reports that actually get read
Our reports are designed for action. Clear executive summaries, prioritized findings, and practical remediation steps.

What's Included in Every Report
Executive Summary
Board-ready summary with business impact.
Prioritized Findings
Findings ranked by risk level.
Remediation Steps
Step-by-step fix guidance.
Proof of Concept
Evidence and PoC details.
Trend Analysis
Historical comparison data.
Comprehensive security testing
From web applications to cloud and infrastructure, we deliver targeted security testing aligned to your risk profile - using proven methodologies designed to surface exploitable weaknesses and support informed decision-making.
Black Box
No prior knowledge. We simulate a real external attacker with zero internal information.
Grey Box
Partial access. We test like a compromised insider or partner with limited credentials.
White Box
Full transparency. We perform deep analysis with complete access to architecture and code.
Red Team
Full adversarial simulation testing your people, processes, and technology.
Security testing across your stack
Web Application Testing
Detailed assessment of your web applications against OWASP Top 10 and beyond.
Infrastructure Testing
Network and server-side security assessment of your internal and external infrastructure.
Cloud Security Assessment
Security review of AWS, Azure, GCP, or multi-cloud environments.
Mobile Application Testing
Security assessment of iOS and Android applications including their backends.
API & Microservices
Focused testing of your APIs, including REST, GraphQL, and microservices architecture.
Social Engineering
Test your human defenses with controlled phishing, vishing, and physical security tests.
How our Red Team platform works
A collaborative process designed to deliver maximum value with minimum disruption.
Scope Together
Define your testing scope collaboratively. Upload assets, set priorities, and agree on approach - all in one place.
Expert Testing
Our certified testers execute thorough assessments while you track progress in real-time.
Clear Reporting
Receive actionable findings prioritized by business impact, with step-by-step remediation guidance.
Track & Verify
Manage remediation, request retests, and watch your security score improve over time.
Services powered by our Red Team Platform
Every offensive security engagement includes full platform access for complete transparency.
Red Team Services
Find vulnerabilities before attackers do with real-world attack simulations.
- Penetration Testing (Web, Mobile, Cloud, Network)
- Red Team Operations & Adversary Simulation
- Application & Code Security Reviews
Blue Team Services
24/7 threat hunting, rapid containment, and security operations.
- SOC-as-a-Service & Managed Detection
- Incident Response & Digital Forensics
- Threat Intelligence & Defensive Engineering
Education & Training
Build skills with hands-on training and realistic exercises.
- Technical Red/Blue Team Trainings
- Cyber Range, CTF & Attack Simulations
- Security Awareness & Phishing Campaigns
Consultancy & GRC
Strategic guidance for long-term cyber resilience and compliance.
- Governance, Risk & Compliance (NIS2, ISO)
- Security Strategy & CISO-as-a-Service
- Architecture & Digital Transformation
Your security data, protected. protected
Vulnerability information is sensitive. We handle it with the same level of security we recommend to you. Your data never leaves our secure environment.
- Secure hosting in EU data centers
- Multi-factor authentication on all accounts
- Granular permission controls
- Complete audit logging
- Data retention policies tailored to your needs
- SOC 2 certified environment
Frequently asked questions
Red Team Cockpit serves both security teams and organizations. Security teams benefit from streamlined workflows, AI-assisted reporting, and real-time collaboration, while companies gain actionable insights, continuous risk validation, and executive-ready reports for better decision-making.
Red Team Cockpit supports all major testing types:
Black Box: simulates an external attacker with no prior knowledge.
Grey Box: partial knowledge provided to testers.
White Box: full access to code and architecture.
Red Team: full-scope adversary simulation including social engineering, lateral movement, and real-world attack scenarios.
Yes. It supports imports from popular tools like Nessus, Nuclei, Burp Suite, and Nmap. Automatic parsing, deduplication, and severity mapping help maintain workflow efficiency.
The platform automates documentation using AI, structured templates, and one-click export options (PDF/DOCX). It ensures consistent, professional, and executive-ready reports while saving time on manual work.
Red Team Cockpit is suitable for finance, healthcare, technology, manufacturing, retail, and government sectors. It aligns with standards such as PCI-DSS, ISO 27001, SOC 2, NIS2, DORA, GDPR, and HIPAA, helping organizations meet regulatory obligations.
Enterprise-grade security controls are built in, including AES-256 encrypted credential storage, end-to-end encryption, role-based access, two-factor authentication, IP whitelisting, audit logging, and SSO/SAML support.
Ready to transform your pentesting workflow?
Join hundreds of security professionals who trust Red Team Cockpit. Schedule a demo to see how we can help your team.