Gain complete visibility into your security operations.
When threats emerge, every second counts. Defense Command platform provides real-time visibility across alerts, investigations, and response actions - giving security teams continuous situational awareness, 24/7.
The challenges you face
Security operations grow more complex as environments scale. These are the gaps we help organizations close every day.
Alert fatigue
Thousands of alerts daily with no clear way to separate noise from genuine threats.
Slow response times
Hours or days between detection and containment puts your business at risk.
Blind spots
Limited visibility into what your security team is actually doing and finding.
Communication gaps
Critical updates lost in email threads, unclear escalation paths during incidents.
Tool sprawl
Dozens of security tools with no unified view of your security posture.
Measuring ROI
Difficulty demonstrating the value of security investments to leadership.
Gain full visibility into your Security Operations
Our Defense Command platform delivers continuous transparency across alerts, investigations, and response actions - ensuring security leaders understand what is happening and why it matters.
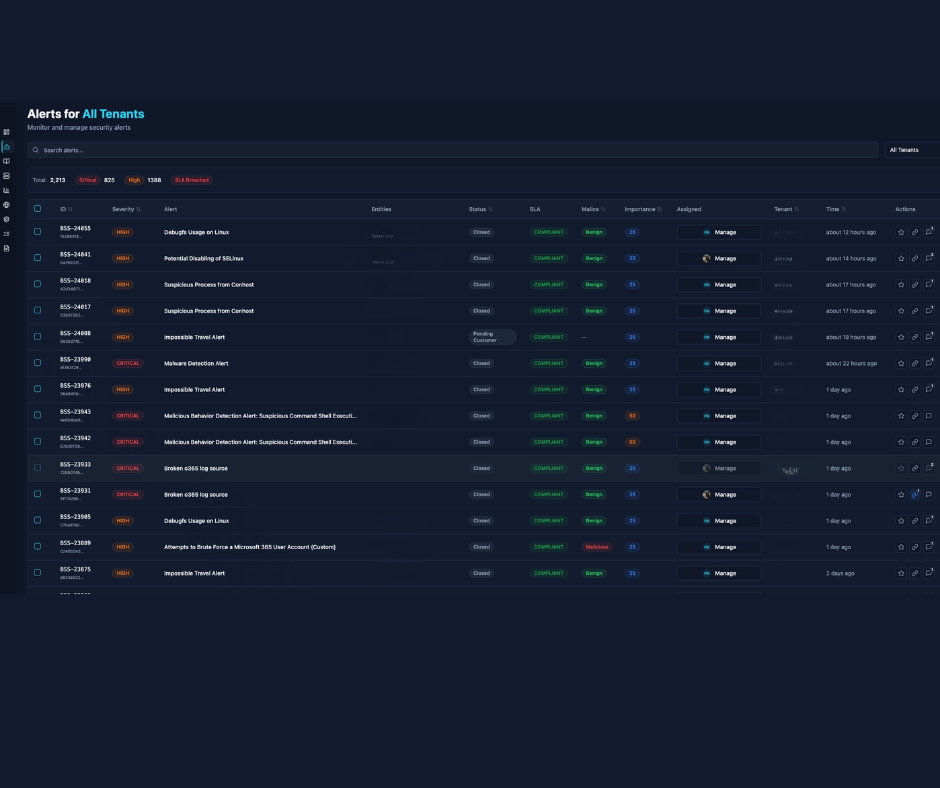
Intelligent alert triage
Every alert enriched with context, severity scoring, and recommended actions. Know exactly what needs your attention.
- Automated enrichment
- Priority scoring
- False positive reduction
Real-time threat visibility
Watch your security operations in real-time. See active investigations, response actions, and threat trends at a glance.
- Live dashboards
- Threat analytics
- Trend visualization
Incident timeline
Complete chronological view of every incident, from first detection through resolution. Never lose track of what happened.
- Full event history
- Action logging
- Evidence collection
Health monitoring
Know your security posture at all times. Monitor sensor health, coverage gaps, and detection efficacy.
- Coverage metrics
- Sensor health
- Performance KPIs
Seamless collaboration
Built-in communication channels between your team and ours. Ask questions, request actions, get updates, all in context.
- In-context chat
- Assignment workflow
- Notification controls
Compliance ready
Automated reporting for compliance requirements. Generate evidence packages for audits with one click.
- Compliance reports
- Audit trails
- Evidence packages
A unified Defense Command Center for your Security Operations
One centralized platform that brings alerts, investigations, and response actions together - so teams can act faster and with confidence.
Active Incidents
3
Alerts Today
127
Avg Response
< 12min
Coverage
98.7%
Recent Alerts
Suspicious login attempt detected
2 min ago
Unusual outbound traffic pattern
15 min ago
New device enrolled in MDM
1 hour ago
Activity
847
Events This Hour
What our security analysts deliver
Beyond monitoring? Proactive threat hunting, rapid response, and continuous security improvement - designed for enterprise environments.
Threat Hunting
Proactive searching for threats that evade automated detection.
Rapid Response
Immediate containment actions when threats are confirmed.
Log Analysis
Deep analysis of security logs across your entire environment.
Vulnerability Context
Integration with vulnerability data for threat prioritization.
Threat Intelligence
Real-time threat intel tailored to your industry and environment.
Detection Engineering
Continuous improvement of detection rules and coverage.
How our Defense Command delivers security outcomes
From onboarding and integration through continuous protection, the Defense Command platform delivers structured, transparent security operations with minimal operational overhead.
Connect
Integrate your security tools and data sources. We'll ensure complete visibility across your environment.
Monitor
Our analysts watch your environment 24/7, investigating every suspicious activity and potential threat.
Respond
When threats are confirmed, we take immediate containment actions and keep you informed every step of the way.
Improve
Continuous tuning, threat hunting, and recommendations to strengthen your security posture over time.
Services powered by Defense Command
Every defensive security engagement includes full portal access for complete transparency.
Managed Detection & Response
24/7 threat monitoring, hunting, and response with complete visibility through Defense Command.
SOC-as-a-Service
Dedicated security operations team with real-time collaboration and escalation management.
Incident Response
Rapid response to active threats with complete incident documentation and timeline visibility.
Threat Intelligence
Tailored threat intel integrated into your portal, focused on your industry and threat landscape.
Security metrics that matter matter
We track the metrics that matter to security leaders - measuring detection, response, and containment performance, as well as how your security posture improves over time. All metrics are continuously updated and available in your platform dashboard.
- Mean time to detection (MTTD)
- Mean time to response (MTTR)
- Alert-to-investigation ratio
- Threat containment effectiveness
- Coverage and sensor health metrics
- Monthly security posture trends
Frequently asked questions
Unlike traditional tools that generate alerts in isolation, Defense Command provides a centralized, real-time view of all alerts, investigations, and response actions, giving teams continuous situational awareness across their entire environment.
Each alert is automatically enriched with context, severity scoring, and recommended actions, so teams can focus on genuine threats rather than sifting through noise. False positives are minimized, saving time and resources.
Yes. Defense Command offers real-time dashboards, threat analytics, trend visualizations, and incident timelines, allowing you to see active investigations, response actions, and emerging threats at a glance.
All security actions are logged automatically. You can generate audit-ready reports, compliance evidence packages, and full incident histories with one click, simplifying regulatory requirements.
Our security analysts proactively hunt threats, investigate suspicious activity, and take immediate containment actions when required. They also provide continuous recommendations to strengthen your security posture over time.
Defense Command continuously tunes detection rules, hunts for hidden threats, and identifies coverage gaps, ensuring your security operations adapt as your environment grows and threats evolve.
Enterprises with complex IT environments, multiple tools, or distributed teams gain the most. The platform unifies visibility, improves response times, and ensures leadership can clearly see ROI and security effectiveness.
Ready to see your security operations clearly?
Let's discuss your security monitoring needs. We'll show you how our Defense Command transforms security operations into complete visibility.