Penetration Testing That Actually Matters
Go beyond checkbox compliance. Our expert-led penetration tests simulate real-world attacks to find vulnerabilities that automated scanners miss.

The cybersecurity challenges you're facing
Whether you're a CISO building a security program, an IT leader managing risk, or an executive answering to the board - we've helped organizations like yours.
Compliance requirements are mounting
SOC 2, ISO 27001, PCI-DSS, HIPAA. Regulators and customers demand proof of your security posture.
You’re unaware of your blind spots
Hidden vulnerabilities in your systems could be exploited tomorrow. Uncertainty is your biggest risk.
Internal teams are stretched thin
Your security team is busy keeping lights on. Deep-dive testing requires specialized expertise.
Board and stakeholders want assurance
Leadership needs confidence that critical assets are protected. "We think we're secure" isn't enough.
Previous tests didn't deliver value
PDF reports that gathered dust, generic findings, no clear path to improvement.
Third-party risk is increasing
Your vendors, APIs, and integrations expand your attack surface. Supply chain attacks are rising.
Benefits that matter to your
Cybersecurity insights that translate across the organization, from technical teams to the boardroom.
Complete visibility into your risk
Understand exactly where you're vulnerable and what attackers could exploit.
Detailed technical findings with reproduction steps and evidence
Clear risk ratings tied to business impact and financial exposure
Actionable, prioritized findings
Not all vulnerabilities are equal. We rank findings by real-world exploitability and business impact.
CVSS scoring, attack chain analysis, and remediation code samples
Resource allocation guidance and risk reduction roadmaps
Meet compliance requirements
Satisfy audit requirements and demonstrate due diligence to regulators, customers, and partners.
Mappings to OWASP, NIST, CIS, and industry frameworks
Audit-ready reports and compliance attestation letters
Measurable security improvement
Track your security posture over time. See how remediation efforts translate to reduced risk.
Vulnerability trending, retest verification, and regression tracking
Security scorecards and progress dashboards for leadership
Faster time to remediation
Clear guidance means your team can start fixing issues immediately, not weeks later.
Step-by-step remediation instructions with code examples
Reduced mean-time-to-remediation and lower exposure windows
Competitive advantage
Demonstrate security commitment to customers and partners. Win deals where security is deciding factor.
Technical documentation for customer security questionnaires
Executive summaries suitable for customer and investor communications
Every attack surface, tested
From web applications to industrial control systems - we have specialized expertise across your entire technology stack.
Web Application Testing
Comprehensive assessment of your web applications against OWASP Top 10 and advanced attack vectors.
Mobile Application Testing
iOS and Android security assessment including app internals, data storage, and backend APIs.
API & Microservices
Focused testing of REST, GraphQL, gRPC, and microservices architectures.
SaaS Application Testing
Multi-tenant security assessment for SaaS platforms and cloud-native applications.
External Infrastructure
Perimeter testing of internet-facing systems, services, and entry points.
Internal Network Testing
Assessment from an insider perspective: what happens if an attacker gets past the perimeter?
Wireless Security
Assessment of WiFi networks, rogue access points, and wireless attack vectors.
OT/ICS Security
Operational technology and industrial control system security assessment.
Cloud Security (AWS/Azure/GCP)
Configuration review and attack simulation across major cloud platforms.
Container & Kubernetes
Security assessment of containerized environments and orchestration platforms.
DevSecOps Pipeline
Security review of CI/CD pipelines, build processes, and deployment automation.
AI/LLM Security
Security assessment of AI systems, machine learning models, and LLM integrations.
Source Code Review
Manual and automated analysis of application source code to identify security flaws.
Red Team Operations
Full adversarial simulation testing your people, processes, and technology as a unified target.
These categories represent just a fraction of our testing capabilities. Each engagement includes thousands of individual security checks, both manual and automated. Discuss your specific requirements →
Go beyond penetration testing with Red Team Operations
While penetration testing finds technical vulnerabilities, Red Team operations test your entire security program: people, processes, and technology working together under realistic attack conditions.
- Multi-Vector Attacks: phishing, physical access, and technical exploitation
- Objective-Based Testing: achieve specific goals like accessing CEO email
- Detection & Response Validation: test if your SOC catches attacks
- Executive War Games: tabletop exercises for leadership decision-making
Aligned with your business objectives
Different approaches surface different risks and opportunities. We guide you toward the ones that matter most.
Black Box
We simulate a real external attacker with zero prior knowledge. Just like a threat actor would approach your organization.
- Realistic attack simulation, compliance requirements, external threat assessment
Grey Box
Testing with partial access, like a compromised employee, malicious insider, or partner with limited credentials.
- Insider threat assessment, post-authentication security, privilege escalation testing
White Box
Complete access to architecture, source code, and documentation. Maximum depth and coverage.
- Thorough security review, pre-release testing, maximum vulnerability discovery
Red Team Testing
Full-scope adversary simulation designed to test detection, response, and overall organizational resilience.
- Includes social engineering, privilege escalation, lateral movement, and real-world attack scenarios.
How a penetration test unfolds (standard flow)
Structured, collaborative, and transparent - delivering clear insights and prioritized actions that reduce risk fast.
Discovery & Scoping
We understand your environment, business context, and objectives. Together, we define the scope, rules of engagement, and success criteria.
Reconnaissance & Analysis
Our team gathers intelligence about your target environment: mapping the attack surface, identifying technologies, and planning attack vectors.
Active testing
Hands-on security testing by certified professionals. We identify vulnerabilities, chain findings, and document everything in real-time.
Analysis & Reporting
Findings are analyzed, validated, and translated into actionable recommendations with clear prioritization.
Delivery & Debrief
We present findings to both technical and executive stakeholders, ensuring everyone understands the risks and next steps.
Remediation support & retest
We're here to help. Ask questions about findings, get guidance on fixes, and verify remediation with free retesting.
Actionable deliverables, not just reports
Everything you need to understand your risk, fix issues, and demonstrate security to stakeholders.

What's Included in Every Report
Proof of Concept (PoC)
Working PoC code and screenshots for every finding.
Business impact
Clear explanation of real-world risk and business exposure.
Remediation steps
Detailed fix guidance with code examples and references.
Executive summary
Board-ready summary with risk scores and trends.
Attestation letter
Formal documentation for auditors and compliance.
Free retesting
Verify your remediations with complimentary retesting.
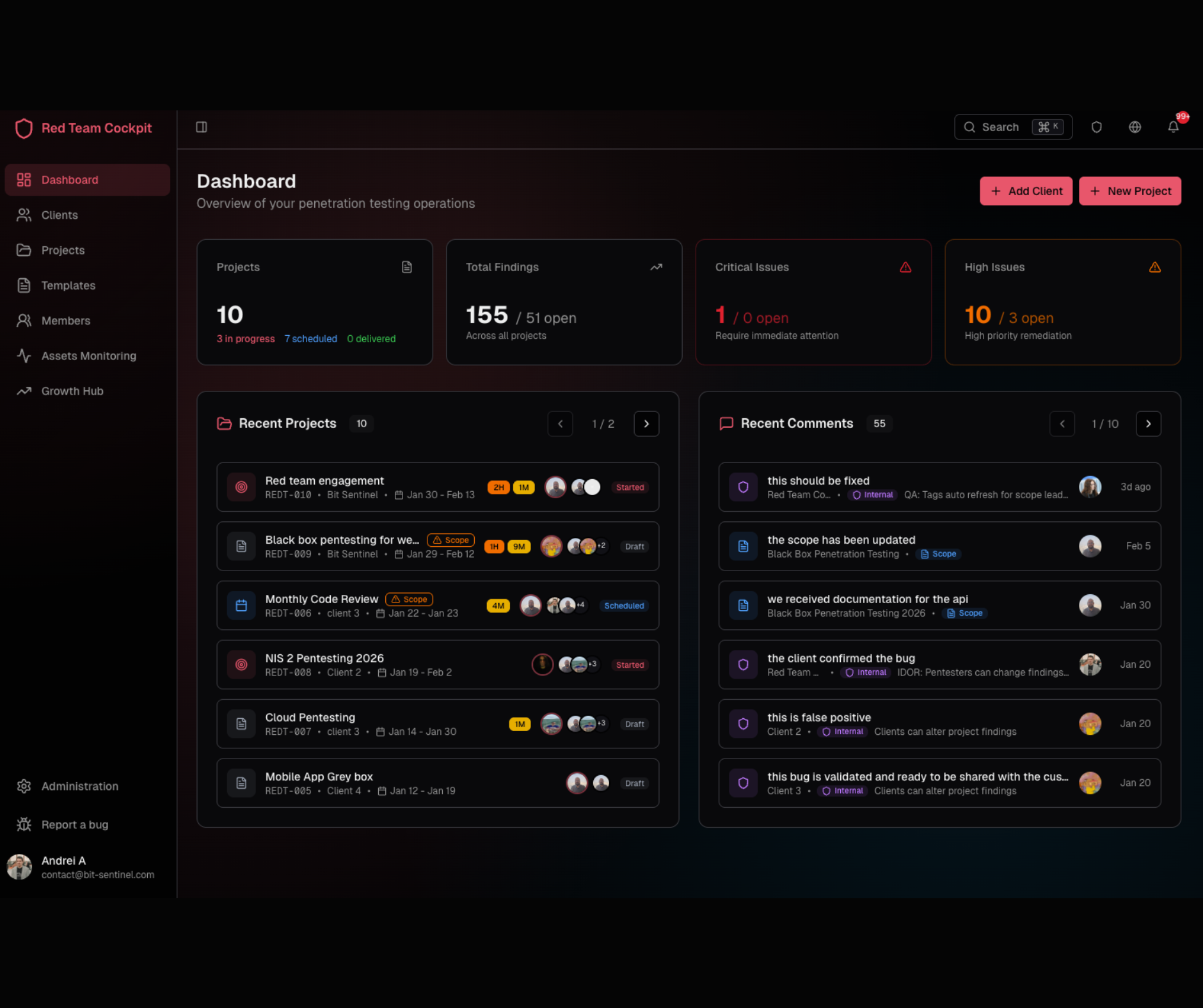
Your dedicated Customer Portal
Get real-time visibility into progress, findings, and remediation, and collaborate directly with our team - with full transparency from start to finish.
Real-time updates
See findings as they're discovered, not weeks later.
Finding management
Filter, sort, and export findings. Assign to team members.
Direct communication
Chat with testers, ask questions, request clarification.
Report downloads
Generate reports on-demand in multiple formats.
Real-time updates
- Critical findings visible within hours, not weeks
- Watch testing progress in real-time
- Immediate notifications for high-severity issues

"When it comes to customer success software, cybersecurity is crucial. And Bit Sentinel did wonders. We’re already at our third collaboration for penetration testing services, as the team continues to impress us with their professionalism and ethics. Their proactive approach and thorough testing have provided us with invaluable insights into our platform’s security. Bit Sentinel’s reliability and clear communication ensure a seamless and efficient process. We can wholeheartedly say that we look forward to continuing our partnership."
George Maicovschi
Chief Technology Officer @Custify
Frequently asked questions
Most engagements take 2-4 weeks from kickoff to final report. The active testing phase typically runs 5-10 business days depending on scope. We can accommodate urgent timelines when needed.
We design our testing to minimize disruption. Dangerous tests (like DoS) are only performed with explicit approval and during maintenance windows. We maintain constant communication and can pause immediately if issues arise.
Our team holds OSCP, OSCE, OSWE, OSEP, CRTO, CREST, and other industry-recognized certifications. Many team members are also active CTF competitors and CVE researchers.
Yes! Every engagement includes free retesting to verify your remediations are effective. We want you to be confident that vulnerabilities are truly resolved.
Absolutely. We provide attestation letters and reports formatted for SOC 2, ISO 27001, PCI-DSS, HIPAA, and other frameworks, such as NIS2, GDPR and local regulations (e.g. ASF, BNR). We can scope engagements specifically for compliance needs.
Three things: 1) Our team's CTF and bug bounty background means we think like real attackers. 2) Real-time portal access keeps you informed throughout. 3) We focus on actionable findings, not padding reports with scanner output.
Secure your future today
Let's discuss your environment, objectives, and how we can help. This will be an honest conversation about your cybersecurity needs.