Application Security Code Review. Find vulnerabilities before attackers exploit them.
Expert-led manual code review combined with SAST/DAST to uncover exploitable vulnerabilities that automated scanners miss - reducing breach risk and supporting compliance requirements.

Application security by the numbers
Most data breaches originate from software vulnerabilities. Secure code has become a critical control for protecting applications, reducing attack surface, and supporting compliance obligations.
Why development teams struggle with application security
Modern SDLCs introduce expanding attack surfaces - from AI-assisted development to third-party dependencies - creating security gaps that increase breach risk and operational exposure.
AI & Vibe coding risks
GitHub Copilot, ChatGPT, and "vibe coding" accelerate development but introduce code no human fully reviewed. AI-generated code often contains hidden vulnerabilities, insecure patterns, and hallucinated APIs.
Developer security gap
Developers are experts in building features, not security. The 100:1 developer-to-security ratio means vulnerabilities slip through every sprint.
Supply chain complexity
Modern applications rely on hundreds of third-party libraries and dependencies. One compromised package can expose your entire stack, as Log4Shell and SolarWinds proved.
Speed vs. security trade-offs
Pressure to ship fast means security reviews get skipped or rushed. Each release accumulates technical debt that eventually becomes a breach.
Scanner blind spots
Automated SAST/DAST tools generate false positives and miss business logic flaws, authentication bypasses, and race conditions. Without expert analysis, critical issues go undetected.
Legacy code burden
Inherited codebases contain years of accumulated vulnerabilities. No one remembers why security decisions were or were not made.
Compliance mandates
PCI-DSS, SOC 2, ISO 27001, HIPAA, and GDPR all require demonstrable secure development practices. Auditors demand evidence of code security.
Outsourced development
Third-party developers and agencies build code without visibility into your security standards. Trust but verify: external code needs independent review.
Frequent technology changes
New frameworks, languages, and paradigms emerge constantly. Security teams struggle to keep expertise current across an ever-expanding landscape.
6 ways Code Review makes security a competitive differentiator
Security code review turns application security into a measurable advantage - reducing exposure, accelerating delivery, and building trust with customers and regulators.
Detect vulnerabilities early
Find and fix security issues during development, not after attackers exploit them in production.
Catch OWASP Top 10, injection flaws, and logic bugs before they reach production
Reduce breach risk and avoid costly incident response
Reduce remediation costs
Fixing vulnerabilities in the design phase is 100x cheaper.
Fix issues when context is fresh and code is still being worked on
Lower total cost of ownership for application security
Increase code visibility
Gain deep understanding of how your applications work from a security perspective.
Understand security implications of architectural decisions
Make informed decisions about technical investments
Build security into SDLC
Regular reviews embed security best practices into your development culture.
Learn from expert feedback and improve secure coding skills
Demonstrate due diligence and mature security practices
Validate third-party code
Ensure outsourced development and open-source components meet your security standards.
Verify vendor code quality and dependency security
Reduce supply chain risk and vendor liability
Support compliance
Provide evidence of secure development practices for auditors and certification bodies.
Generate documentation required for PCI-DSS, SOC 2, ISO 27001
Satisfy regulatory requirements and customer security questionnaires
Advanced AppSec safeguard modules
We combine multiple security testing methodologies to deliver comprehensive, end-to-end coverage across your application security posture.
Expert Human Analysis
Our security engineers manually review your source code line-by-line, identifying vulnerabilities that automated tools miss. We analyze business logic, authentication flows, authorization controls, and data handling.
Contact UsStatic Application Security Testing
We scan your source code, bytecode, or binaries without executing the application. Our tools analyze code paths, data flows, and patterns to identify potential vulnerabilities early in development.
See HowDynamic Application Security Testing
We test your running application from the outside, simulating real attacker behavior. DAST identifies vulnerabilities visible at runtime that static analysis might miss.
Work With UsArchitectural Security Analysis
We analyze your application architecture to identify potential threats before writing a single line of code. Threat modeling helps you design security in from the start.
Start TodayiOS & Android Application Review
Specialized security review for mobile applications covering both client-side vulnerabilities and API interactions. We test against OWASP Mobile Top 10.
Start TestingREST & GraphQL API Testing
Comprehensive security assessment of your APIs covering authentication, authorization, input validation, and business logic. We test against OWASP API Security Top 10.
Get In TouchHow our security code review is delivered
A structured review process that integrates automated testing and expert analysis to reduce application risk and support compliance requirements.
Scoping & Planning
We understand your application architecture, technology stack, and security concerns. Together we define scope, access requirements, and timeline.
Automated analysis
We run enterprise-grade SAST tools across your codebase to identify common vulnerability patterns and create a baseline for manual analysis.
Manual code review
Our security engineers dive deep into your code, focusing on high-risk areas, authentication flows, data handling, and business logic.
Dynamic testing
We complement static analysis with runtime testing, verifying vulnerabilities are exploitable and identifying issues only visible during execution.
Analysis & Reporting
We analyze all findings, eliminate false positives, prioritize by risk, and create comprehensive documentation with remediation guidance.
Delivery & Support
We present findings to your team, answer questions, and provide ongoing support during remediation including free retesting.
Comprehensive code review findings with actionable security fixes
Every engagement produces detailed documentation that enables your team to understand, prioritize, and remediate identified vulnerabilities.
Executive summary
High-level overview for leadership with risk ratings, business impact, and strategic recommendations.
- Risk posture score
- Business impact analysis
- Strategic recommendations
- Compliance mapping
Technical findings report
Detailed vulnerability documentation with affected code locations, exploitation scenarios, and proof of concept.
- Code snippets
- Exploitation steps
- CVSS scoring
- CWE classification
- File and line references
Remediation guidance
Step-by-step fix instructions for each vulnerability with secure code examples in your language.
- Fix code samples
- Library recommendations
- Configuration changes
- Testing procedures
SAST/DAST scan results
Full automated tool output with false positives removed and findings correlated with manual analysis.
- Dependency vulnerabilities
- Code quality metrics
- Coverage reports
- Trending analysis
Security architecture review
Assessment of your application architecture with recommendations for security improvements.
- Threat model diagram
- Trust boundaries
- Data flow analysis
- Design recommendations
Retesting & attestation
Free retesting to verify remediations and formal attestation letter for compliance requirements.
- Verification testing
- Attestation letter
- Delta report
- Compliance evidence
20+
Security Experts
24/7
Monitoring
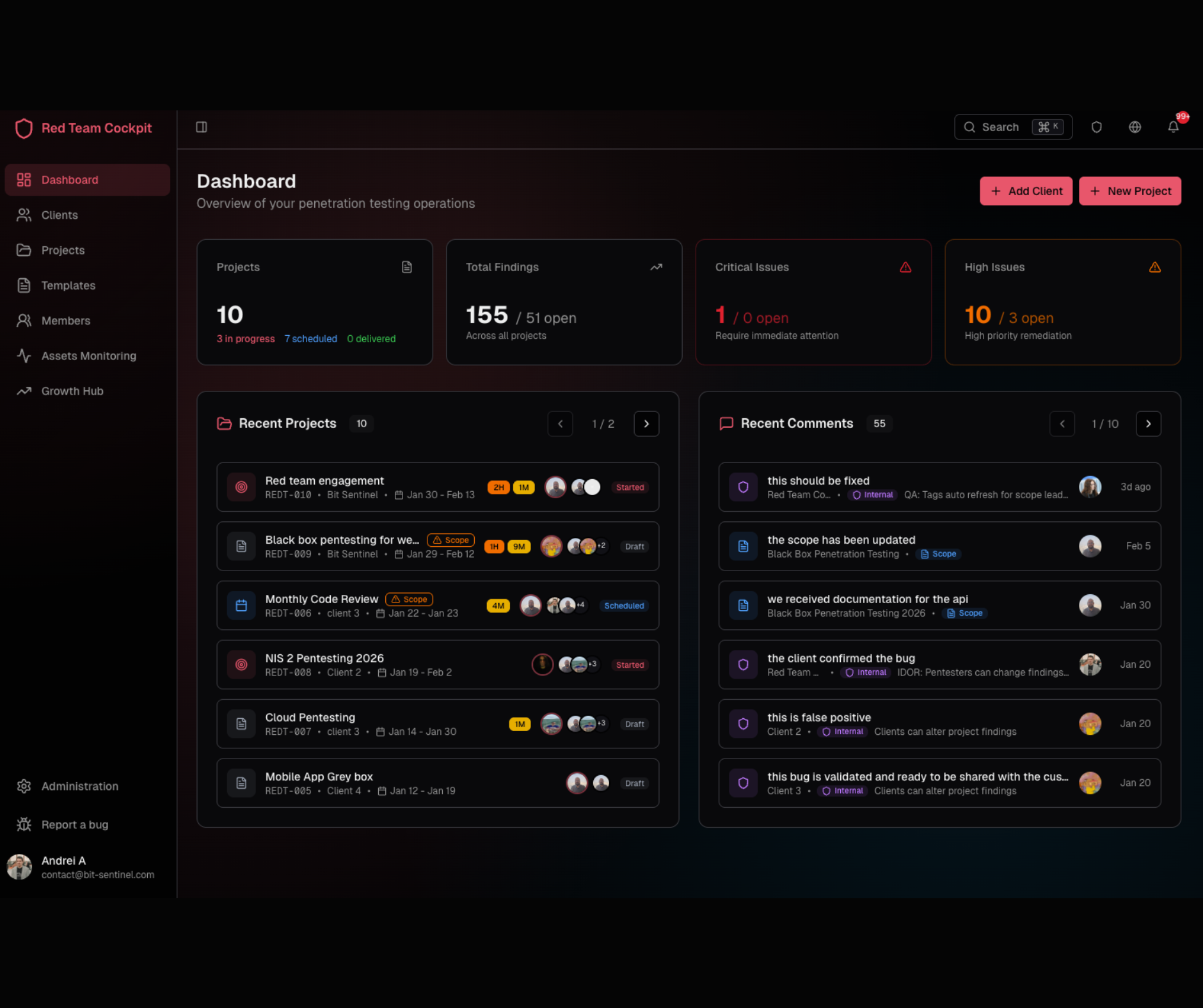
Track progress in your portal
Access findings as they're discovered through our Red Team Cockpit. No need to wait for the final report: you can see vulnerabilities in real-time.
- Live findings feed as issues are discovered
- Code snippets with syntax highlighting
- Direct communication with reviewers
- Export reports in multiple formats
Programming languages & frameworks we cover
Our security engineers have deep expertise across 100+ programming languages and frameworks. From mainstream enterprise stacks to specialized and legacy technologies, we've got you covered.
JavaScript/TypeScript
Node.js, React, Angular, Vue.js, Next.js, Express, Deno, Svelte
Python
Django, Flask, FastAPI, Tornado, Pyramid, Celery, SQLAlchemy
Java
Spring Boot, Jakarta EE, Struts, Hibernate, Gradle, Maven, Micronaut
C# / .NET
.NET Core, ASP.NET, Blazor, Entity Framework, MAUI, WPF, WinForms
PHP
Laravel, Symfony, WordPress, Drupal, Magento, CodeIgniter, Yii
Ruby
Ruby on Rails, Sinatra, Hanami, Grape, RSpec
Go (Golang)
Gin, Echo, Fiber, Chi, gRPC, Gorilla, Hugo
Rust
Actix, Axum, Rocket, Tokio, WebAssembly
C / C++
Qt, Boost, STL, Embedded Systems, Linux Kernel
Mobile (iOS)
Swift, SwiftUI, Objective-C, Xcode, Combine
Mobile (Android)
Kotlin, Java, Jetpack Compose, Android Studio
Cross-Platform
React Native, Flutter, Xamarin, Ionic, Electron
Scripting Languages
Bash, PowerShell, Perl, Lua, Groovy, Tcl
Data & ML
R, Scala, Julia, MATLAB, TensorFlow, PyTorch
Legacy Systems
COBOL, Fortran, Delphi, VB6, Classic ASP
Smart Contracts
Solidity, Vyper, Rust (Solana), Move, Cairo
Frequently asked questions
Typical engagements run 2-3 weeks for small to medium applications, including automated scanning, manual review, and reporting. Larger codebases or multiple applications may take longer.
We provide accurate timelines after our initial scoping call
We typically need read-only access to your source code repository (GitHub, GitLab, Bitbucket, etc.). For DAST testing, we need access to a staging environment. We sign NDAs and can work within your security requirements.
Automated tools (SAST/DAST) are excellent at finding common vulnerability patterns but generate false positives and miss business logic flaws. Manual review catches architectural issues, authentication bypass, race conditions, and logic flaws that scanners cannot identify.
We have expertise in all major languages including JavaScript/TypeScript, Python, Java, C#, PHP, Ruby, Go, Swift, and Kotlin. Our team can also review less common languages. Contact us to discuss your specific stack.
We test against OWASP Top 10, OWASP API Security Top 10, OWASP Mobile Top 10, CWE/SANS Top 25, and your specific compliance requirements (PCI-DSS, SOC 2, ISO 27001, HIPAA, etc.).
We treat your code with the same care as our own. All reviews are conducted by vetted security engineers under NDA. We can work within your VPN, use your secure collaboration tools, or conduct on-site reviews if required.
Yes! Every engagement includes free retesting to verify your remediations are effective. We provide updated reports showing resolved findings and any new issues introduced during fixes.
Absolutely. We can help you implement SAST tools in your CI/CD pipeline for continuous security testing. We also offer ongoing advisory services to review scan results and triage findings.
"We started working with Bit Sentinel two years ago when we needed to perform a penetration testing audit & a security code review. The team succeeded to offer quality services in due time so we developed the collaboration over the years. Last year they also helped us in the process of becoming GDPR compliant. We even recommend their services to our customers as they are professional and very transparent, always proactive and trustworthy."
Doru VIJIIANU
CEO @Zipper Services
Security expertise you can trust
Our code reviewers are active security researchers with real-world offensive experience
Ready to secure your application code?
Don't wait for attackers to find your vulnerabilities. Our expert security engineers will analyze your code and provide actionable remediation guidance.